with CipherBox
Watch Now!
Nowadays, nearly every worker who can, is working working remotely to get the job done. Employees need to use new tools to communicate and collaborate. Other business technology functions are moving away being processed locally. These tools rely on Cloud technology to work. More and more companies are migrating to the Cloud.
We covered how IT leaders can secure these systems. The main topics included:
 Shared Cloud Responsibility Model
Shared Cloud Responsibility Model
The security of your systems in the Cloud are dependent on both the provider and the customers. Learn how this model works.
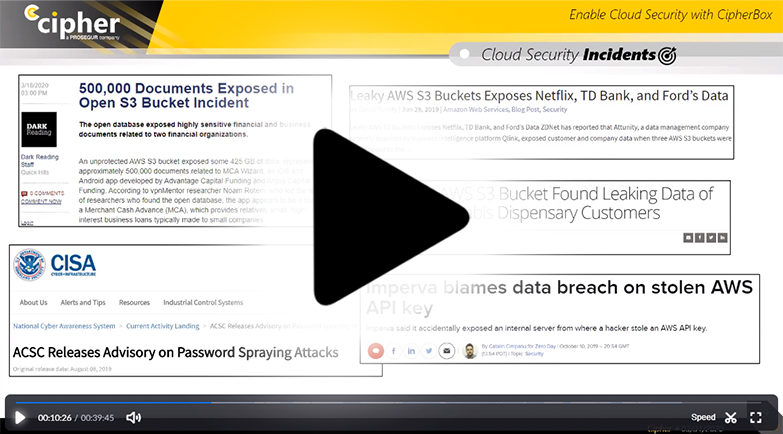
 Top Cloud Security Threats
Top Cloud Security Threats
The increasing move from local databases to cloud allows for more opportunities for human error and hacker ingenuity to result in breaches.
 Best Practice for Securing Cloud
Best Practice for Securing Cloud
Industry groups and Cloud providers like Amazon and Google have provided guidance on the step-by-step process to secure your Cloud.
 How to Secure your Cloud with CipherBox
How to Secure your Cloud with CipherBox
CipherBox is tailored to monitoring your infrastructure in the Cloud. Learn how it can save time and keep your company secure.

Monitoring & Response
Security Information and Event Management (SIEM) and Log Management technologies focused on fast threat detection and incident response.Endpoint
Detection
Endpoint Detection and Response (EDR) technology focused on delivering efficient endpoint monitoring, either if the endpoints are inside or outside your premises or network.
Network
Detection
Network Intrusion Detection System (IDS) technology focused on delivering efficient network threat detection to monitor suspicious activities happening in your environment.
Vulnerability Management
Asset Discovery and Vulnerability Management (VM) technologies focused on discovering the assets connected to your network and performing continuous vulnerability assessments.

